1、意大利开发支持IPv6的新型IoT僵尸网络
标题:Exclusive: MalwareMustDie spotted a new IoT Linux/IRCTelnet malware made in Italy
作者信息:October 29, 2016 By Pierluigi Paganini
//BEGIN
Exclusive: The security researcher MalwareMustDie has found a new Linux/IRCTelnet malware– made in Italy – that aims IoT botnet connected by IRC and Telnet. It is able to generate an IPv6 DDoS and performing NEW dangerous capabilities that Mirai was unable to cover.
In a brief interview to Security Affairs @unixfreakjp of MalwareMustDie group explains which are the main characteristics in order to be able to fight against this new malware with a proper security awareness.
安全专家首次发现恶意代码利用物联网IoT设备采用IPv6协议进而发起DDOS攻击。从代码的分析来看,该ELF恶意代码很像出自意大利。僵尸网络是通过IRC以及Telnet进行连接的。与风头正紧的Mirai(未来)IoT恶意代码相比,这个恶意代码填补了其空缺。本文诠释了一些常见问题,以便能采用合适的安全策略来对付这个新的恶意代码。目前该恶意代码被临时命名为:Linux/IRCTelenet。
//END
First question:
Do you think that Linux/IRCTelenet is more dangerous than Mirai?
Mirai is dangerous in its own way. With new DDoS attack functions, low awareness, and hard to fetch the sample. Also with AV that was not using MIRAI as the new name but sticks with an old name of malware…it is lowering the security alert response. So when it hit hard, people get surprised.
Second Question:
What are the capability of the “IP spoof option in IPv4 or IPv6”?
When an infected IoT is performing attack, in example, via UDP6 or TCP6, Linux/IRCTelnet is having a option to spoof the source IP of the attacker (itself’s IP) for not revealing the original IP in the generated packet used to flood the target
Third Question:
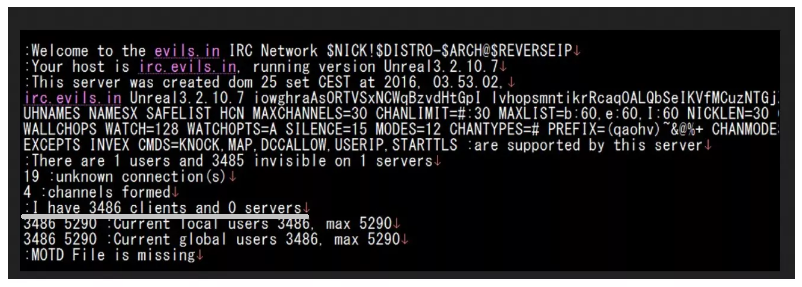
How do you know that the usable bot in this new botnet is about 3500?
A. I show you a figure:
Fourth Question:
Q. Do you think this malware is originally coded?
A. After further analysis comparing the overall done reversed code to the historically detected ELF malware botnet, we found a very good match, that confirms the source code used for this botnet is based on the root of Aidra botnet. I was not so sure about this until I reversed the whole source code and comparing the overall done reversed code to the historically detected ELF malware botnet libraries. And I found a very good match, along with several modifications and overhaul on original Aidra code. Built based on old codes of legendary Aidra bot, added with new logic of Torlus/Gayfgt’s for telnet scanner and using the Mirai’s leaked vulnerable IoT device’s login credential, is driving a high infection speed of Linux/IRCTelnet, so it can raise almost 3,500 bot clients within only 5 days from the firstly its loader detected. Indeed, the spoofing and IPv6 used was designed and trade mark of Aidra botnet family, and to make a new version of this botnet based on the recent vulnerable threat landscape is really inviting a bad news.. All of the reversed details stayed. I was reversed the malware BEFORE I even know this fact . It is very surprising to see a new type of Aidra botnet in this era, and this botnet is really a re-designed and modified of old Aidra to be a brand new threat landscape that we will face now.
This is the log of the IRC Server, as you see 3486 “users” were connected at that time.
一共4个问题:
1 Linux/IRCTelenet是不是比Mirai(未来)威胁性更大? 答:这两者各有千秋。人们往往会将新出现的恶意代码与以前的恶意代码混淆,因此没有足够的重视。往往直到产生了严重的后果,才意识到:啊,原来这个看起来不起眼的恶意代码,原来如此的厉害。
2 IPv6和IPv4有什么特别的功能:IPv6更容易隐藏自身的真实IP地址,这里只需要简单的采用UDP6和TCP6参数。
3 如何知道目前的感染数量是3500? 答:直接链接到IRC频道,看一组数字截图:
图
4 Linux/IRCTelenet这个恶意代码是全新的?答:经过仔细分析,发现这个新发现的恶意代码与以前的Aidra非常相似,应该是其变种,而不是全新的。当然结合了最新出现的Mirai恶意代码的一些特性。因此经过这些因素的整合,其感染率明显提升:发现的5天内,感染数量就增长到了3500左右。
点评:IoT这是要风起云涌呀..... |